The firewall rules in MerlinWRT just quit working so the table I entered doesn’t do anything. Seems like other people had the same problem too. So if you just use the WebUI, it’s either turning the firewall all on or all off.
There’s a twist in configuring the firewall with iptables in routers: the instruction you got on the Internet often append the entry to the end of the table in the section (they use the -A switch) and they didn’t explicitly tell you that’s what they are doing and what the implications are.
Turns out when you enable the firewall in the router, it enters a table of DROP ALL lines, which is supposed to be a catch all after all the exceptions you spelled out! You are supposed to enter the exceptions BEFORE the default entries set by the router, not append after, so the packet you want to accept gets fished out before it reaches the catch all (drop all) entries entered by the router automatically when you turn on firewall. So the solution is to replace the -A (append) switch with -I (insert) switch
As for putting SoftEther VPN on MerlinWRT, here’s the commands to type in SSH to add the firewall rules to open the port, which is what the broken WebUI interface was supposed to do:
iptables -I INPUT -p tcp -m multiport --dport 443,992,5555,8888 -j ACCEPTThis line opens SoftEther’s standard ports 443,992,5555,8888, all TCP only.
Don’t even think of using iptables-save as the router do not have persistent storage other than /jffs or USB. I suspect iptables-save merely writes to RAM disk so the changes will be lost on next boot.
You’ll need to put this line in /jffs/scripts/firewall-start script instead. If this is a new file, make sure you chmod +x /jffs/scripts/firewall-start to make the file executable.
Well it’s not too bad of a design after-all since it’s a mess to fish out the iptable lines you want to delete, so keeping your changes in a file to be loaded with the firewall on boot is a smart move.
If all your devices downstream that you forward incoming traffic to (aka servers) has firewalls, the built-in firewall mainly protect the router itself, so if it gets too frustrating, it might not be too big of a deal to turn the router’s firewall off.
There’s also another weird behavior that if the port is firewall blocked, the server admin program intermittently still connect but it connects to a blank state server (blank config). WTF!
More bonus: open ports for UDP acceleration
Setup L2TP/IPsec VPN Server on SoftEther VPN Server – SoftEther VPN Project
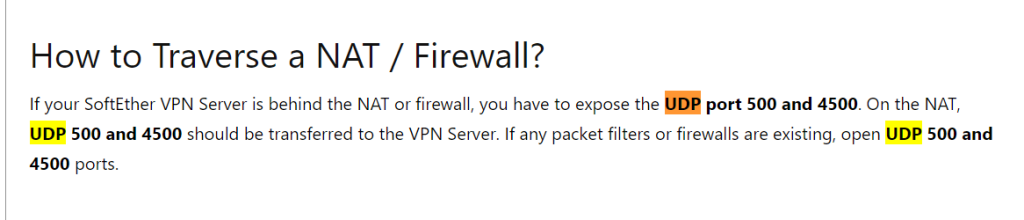
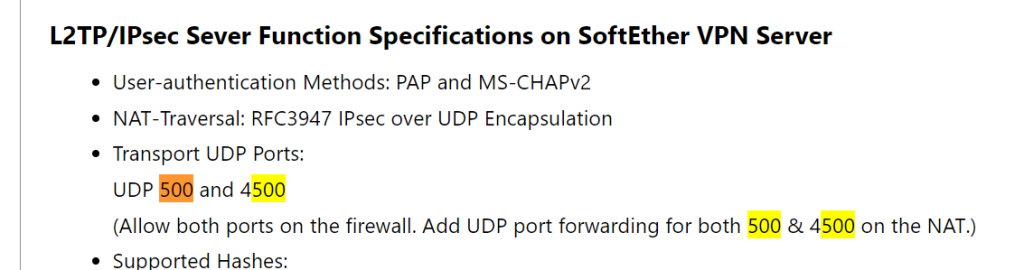
I believe UDP port 500 is IKE and UDP port 4500 is IPSec NAT transverasal, which I think it’s used by L2TP/IPsec if you turn it on.
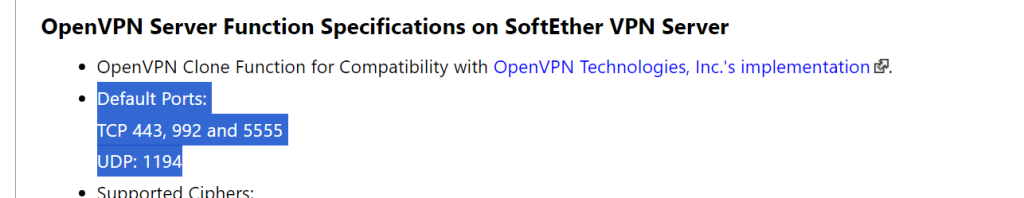
If you use OpenVPN server part of it, open UDP port 1194:
But according to this forum discussion, it simply look up the source code for UDP acceleration to determine the UDP port range they are using:
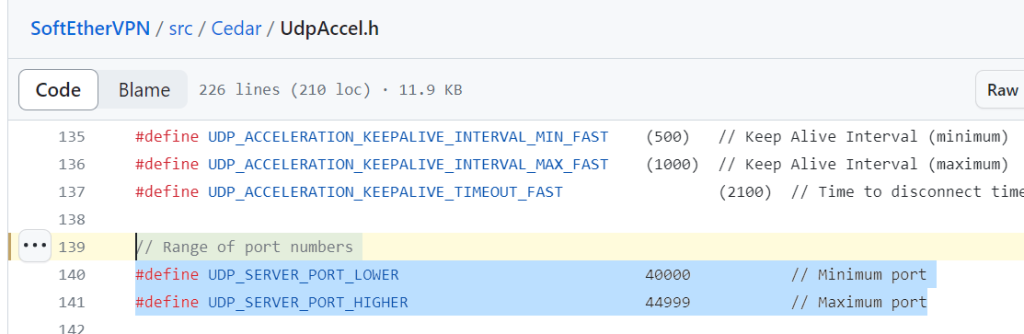
So I’ll add this line to /jffs/scripts/firewall-start to open UDP ports 500,4500,40000:44999 as well
iptables -I INPUT -p udp -m multiport --dport 500,4500,40000:44999 -j ACCEPT ![]()